
Your Phone Number Is a Security Key You Barely Control
Your phone number is often used as proof of identity, but attackers can take it over through SIM swapping or port-out fraud. Here is how the attack works and how to reduce the risk...
15.05.2026
Your phone number is often used as proof of identity, but attackers can take it over through SIM swapping or port-out fraud. Here is how the attack works and how to reduce the risk...
15.05.2026
Cyber attackers are exploiting the promise of new jobs. Fake recruiters and “task” platforms ar...
02.05.2026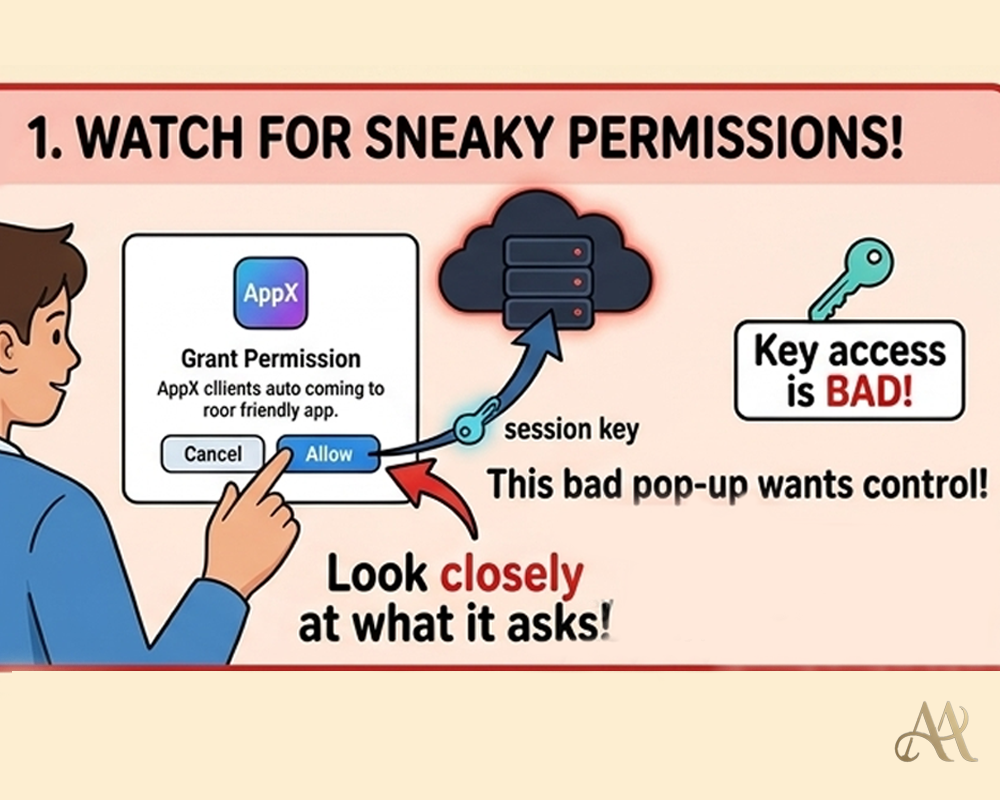
The worst login might be the one you already approved. Learn how attackers steal approved app t...
02.05.2026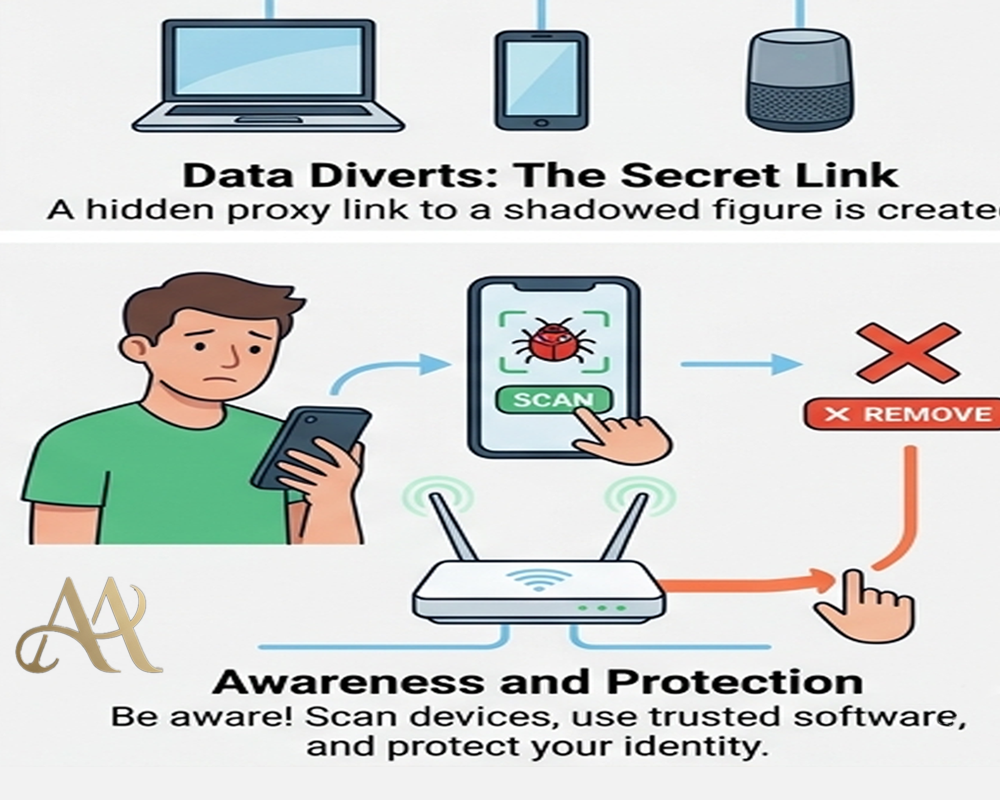
Don’t assume your home network is safe. Cybercriminals now use “residential proxies” to route a...
02.05.2026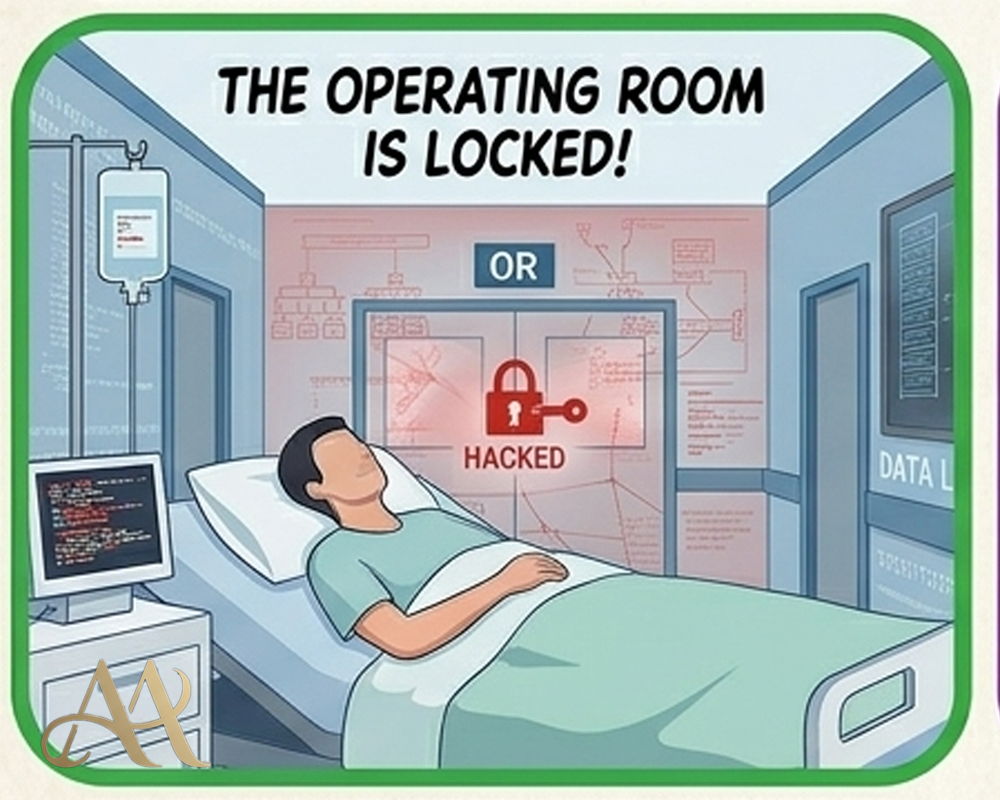
Cyberattacks on hospitals are no longer hypothetical, they delay care, expose data, and endange...
02.05.2026Readers are spending the most time on these posts.
Attackers no longer need your password, they need your session. Learn how session hijacking bypasses MFA and what you can do to stay protected.
Attackers are now tricking users into infecting their own machines through simple copy-paste actions. Here’s how the ClickFix scam works and why it’s more dangerous than it looks.
QR codes feel safe-but they’ve become a growing cybersecurity blind spot. Here’s how QR phishing works and how to protect yourself before you scan.
Extensions often have deep permissions. Learn how malicious add-ons steal your chat logs and browsing history, and how to protect yourself.
Excerpt: Attackers are manipulating Google/Bing results so that trusted-looking software downloads (e.g. VPN clients) actually install malware. Learn how fake “official” downloads are used to steal credentials and how to avoid these traps.
