The worst login might be the one you already approved. Learn how attackers steal approved app tokens to bypass logins and steal data.
Many security teams focus on protecting passwords and multi-factor logins. But the real danger can come from the permissions we’ve already granted. In recent breaches (2025–2026), attackers have stolen long-lived OAuth tokens, session cookies, and integration secrets from approved apps. With these tokens, they bypass login prompts entirely and move laterally across cloud services. This article explains how “approved” apps and tokens work, why attackers target them, and what you can do about it.
What It Is
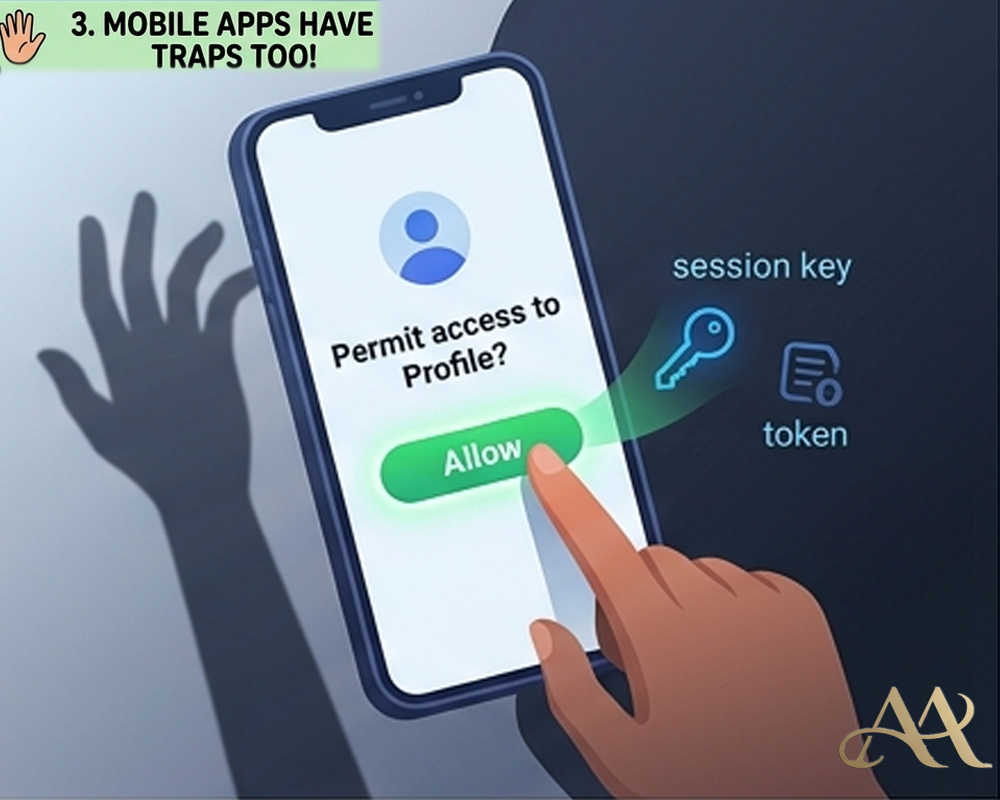
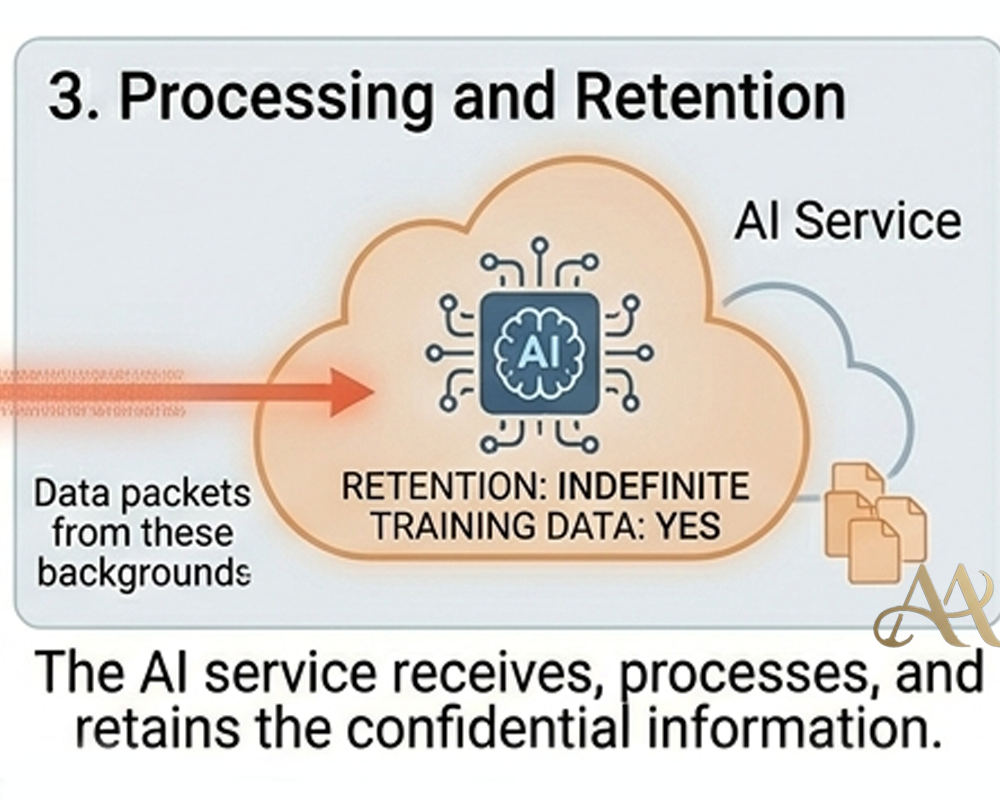
Linked apps and OAuth tokens are the keys you hand out when you click Allow on a permission screen. For example, authorizing a third-party tool in Google Workspace or Salesforce issues that app an OAuth token (and sometimes a browser session cookie) tied to your account. These tokens function like master keys: they prove who you are without re-entering a password. In simple terms, the login or session you approved acts as a persistent pass. Attackers target these tokens because they carry the same trust as a successful login.
How It Works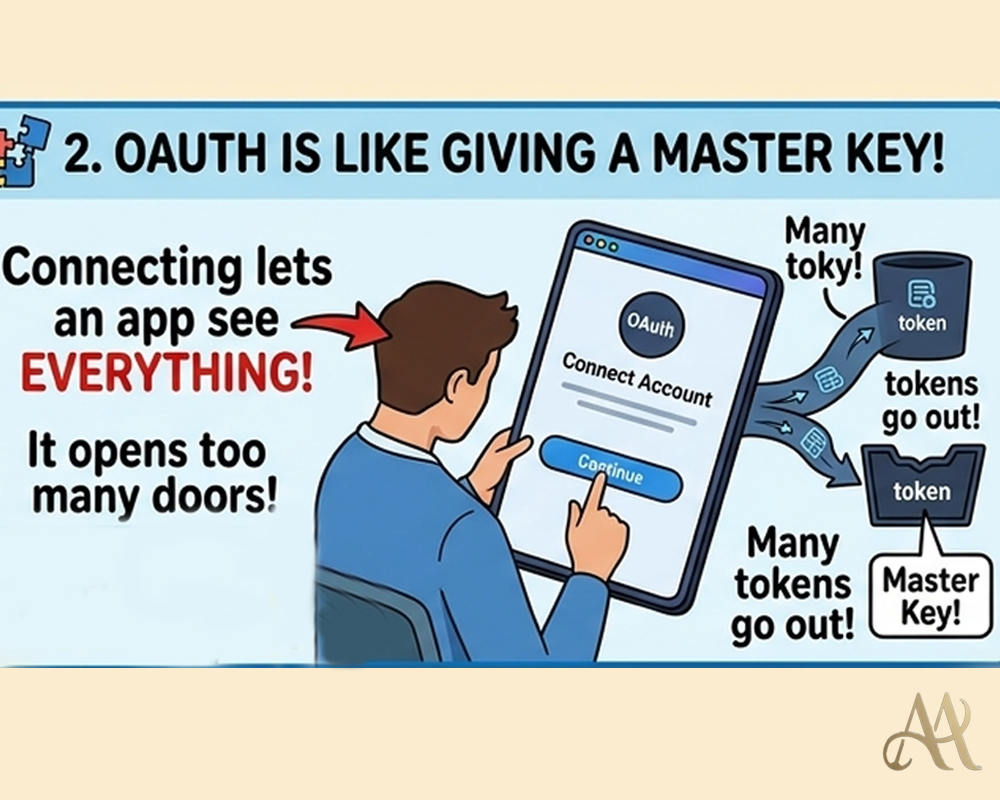 Attackers use several routes to hijack approved tokens. Often it starts with initial access to an authorized app or endpoint through a vendor breach, spearphishing an employee, or malicious browser extension. In the 2025 Salesloft/Drift attack, adversaries broke into Salesloft and stole OAuth tokens that were linked to hundreds of Salesforce instances. These stolen tokens allowed the attackers to run queries and extract data on those orgs without any password or MFA challenge, as if the users themselves were still in control.
Attackers use several routes to hijack approved tokens. Often it starts with initial access to an authorized app or endpoint through a vendor breach, spearphishing an employee, or malicious browser extension. In the 2025 Salesloft/Drift attack, adversaries broke into Salesloft and stole OAuth tokens that were linked to hundreds of Salesforce instances. These stolen tokens allowed the attackers to run queries and extract data on those orgs without any password or MFA challenge, as if the users themselves were still in control.
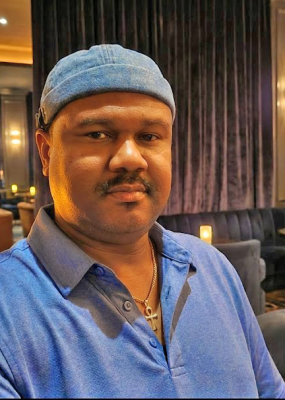
Alternatively, malware on a user’s machine can grab session cookies or refresh tokens directly (akin to MITRE ATT&CK’s Steal Web Session Cookie, T1539). Another trick is abusing OAuth’s redirect features: attackers send a victim through a legitimate login page that silently redirects to a malicious site, capturing the token in the process. Once in possession of a valid token, the attacker’s actions look completely normal to the service, requests come from a “logged-in” user, bypassing MFA and leaving no failed-login alerts. From there, the attacker can access data, call APIs, or even create new tokens and move laterally.
Real-World Impact
- Individuals: A malicious browser extension or app with access to your account can quietly read personal emails, chat history, or cloud files, all through a stolen token. You may never notice until damage is done.
- Businesses: The impact scales dramatically. In the Salesloft breach, attackers harvested API keys, AWS credentials, and customer support data from over 700 companies. They even accessed employee inboxes by using stolen Google Workspace tokens. Similarly, the Vercel incident involved a compromised AI tool’s OAuth token, which gave attackers access to internal systems and environment secrets. Because these attacks exploit existing trust, they can pass as legitimate API activity. They’ve been observed to exfiltrate data at scale while blending into normal traffic.
Systems/Infrastructure: Stolen OAuth tokens effectively become valid credentials. Attackers can escalate privileges, move between services, and even pivot into on-prem systems. This is akin to a supply-chain attack: one compromised app can cascade into many systems (SolarWinds-style) because the permissions already existed.
Common Mistakes or Misconceptions
- Relying only on MFA: It’s often assumed that MFA makes accounts safe. In reality, stolen OAuth/session tokens bypass MFA completely. Once issued, tokens are like bearer cards: no challenge needed.
- Trusting approved apps blindly: Many organizations think “we chose these apps, so they must be safe.” Any app with standing permissions is a potential backdoor. Attackers simply inherit the privileges you granted to the app.
- Ignoring token revocation: Some assume logging out or changing passwords locks attackers out. However, long-lived refresh tokens or OAuth grants can survive password resets, keeping the attacker logged in until those tokens are revoked.
 Practical Defensive Measures
Practical Defensive Measures
- Audit connected apps: Regularly review all third-party applications and permissions in your environment. Revoke unused or unnecessary OAuth grants and enforce least-privilege scopes.
- Use conditional access and CASB: Employ identity and cloud security controls to restrict token use. For example, require trusted devices or locations for OAuth flows, and use cloud app posture tools to detect risky integrations.
- Monitor token usage: Feed logs into your SIEM or cloud monitoring. Look for anomalous behavior like token use from unexpected geographies or large data downloads from an account. As Obsidian notes, behavioral signals (IP changes, unusual data access) are critical to spot token abuse.
- Revoke and rotate tokens: If you suspect a compromise, immediately revoke affected OAuth tokens and refresh tokens. Do not assume a password change is enough.
- User education: Train users to be cautious with consent prompts. Warn them about phishing links that abuse OAuth redirects (e.g. bogus “Microsoft” or “Google” login pages).
Conclusion
In today’s cloud-connected world, the “login” isn’t just what happens at the password prompt, it’s any permission you’ve already granted. Attackers have realized they can ride on existing trust (OAuth tokens, session cookies, API keys) instead of brute-forcing passwords. The lesson is clear: the most dangerous login may indeed be the one you already clicked “Allow” on. Defending against this requires treating every approved app and token as part of your attack surface, regularly auditing permissions, enforcing least privilege, and monitoring token-based activity. By understanding this shift in tactics, organizations can close the hidden gaps in their security and stay one step ahead.
REFERENCE
- https://www.fbi.gov/how-we-can-help-you/scams-and-safety/on-the-internet
- https://www.fbi.gov/how-we-can-help-you/scams-and-safety/common-frauds-and-scams/business-email-compromise




 Attack Anatomy
Attack Anatomy  Digital Deception
Digital Deception 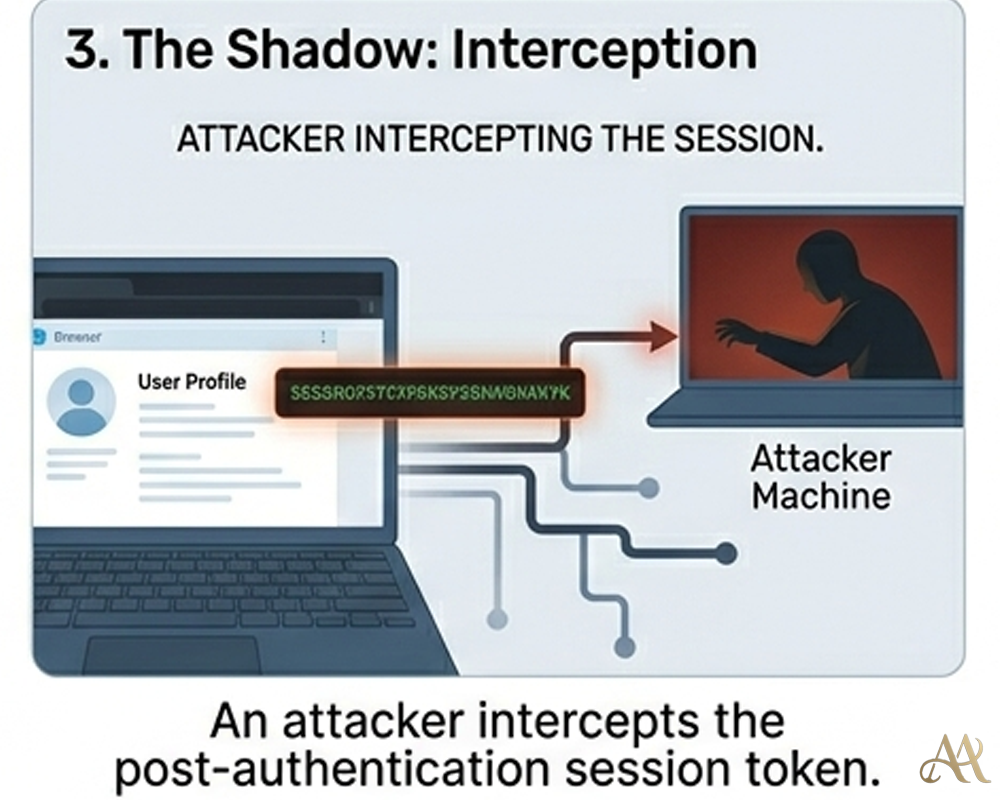
Leave a Reply