Cyber attackers are exploiting the promise of new jobs. Fake recruiters and “task” platforms are tricking job seekers into revealing credentials, paying fees, or running malware. This article explains these threats and how you can stay safe while job hunting.
In an era where millions are job-hunting, cybercriminals have turned the promise of a new opportunity into a trap. Scams targeting job seekers are skyrocketing FTC data show reported losses from online job scams more than tripled between 2020 and 2023, topping $220 million in just the first half of 2024. This surge includes “task scams” and fake recruiter schemes. In this article, we’ll explain how these attacks work, why they matter today, and what steps both individuals and organizations can take to protect themselves.
 Job hunting scams come in several forms but share a common theme: using the lure of work to deceive victims. One common type is the task scam, where fraudsters pose as a gig platform offering simple online tasks (like liking videos or rating products). Initially the app pays out small amounts to build trust, then suddenly asks the user to deposit money to cash out money which is then stolen.
Job hunting scams come in several forms but share a common theme: using the lure of work to deceive victims. One common type is the task scam, where fraudsters pose as a gig platform offering simple online tasks (like liking videos or rating products). Initially the app pays out small amounts to build trust, then suddenly asks the user to deposit money to cash out money which is then stolen.
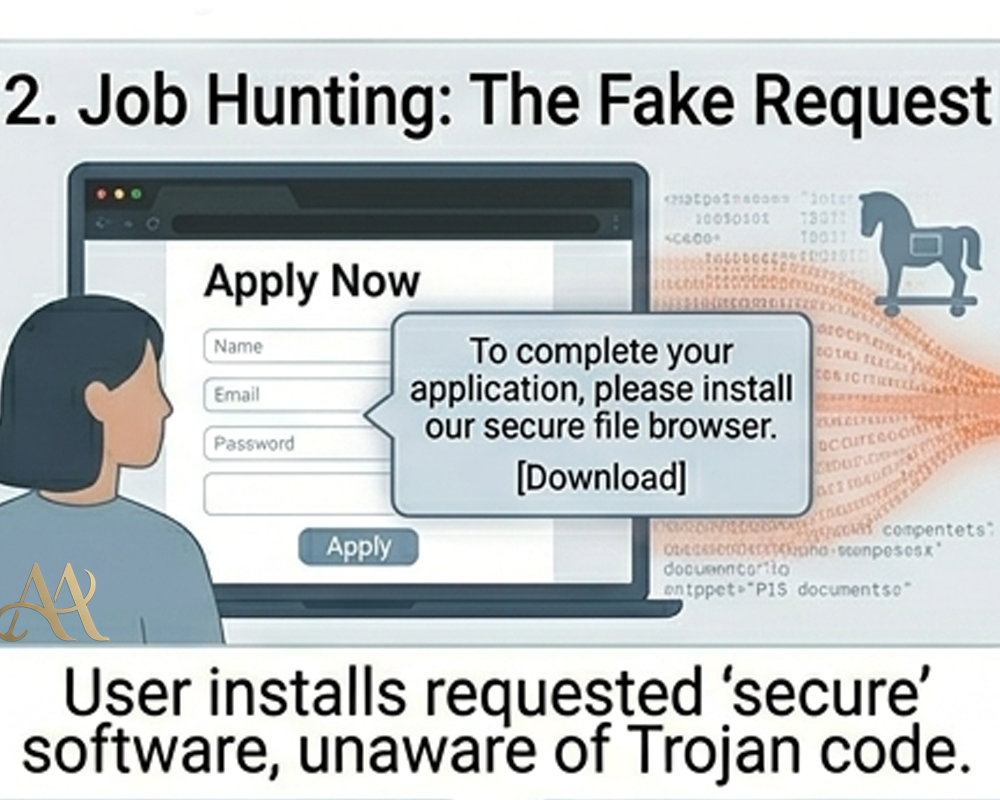
Another type is recruiter impersonation or phishing for credentials. Here, attackers pretend to be recruiters from known companies (even government job postings are faked), luring victims to fake application sites or video interviews. These bogus interviews often hide malware or keyloggers. In short, these schemes are advanced social engineering attacks (akin to phishing) that weaponize the excitement of a job offer
How It Works
- Task Scam Attack Flow: It typically starts with an unsolicited message (on WhatsApp, SMS, or email) offering easy online work. The victim clicks a link to a task app and completes “levels” of tasks, seeing small payouts credited. Then the scammer demands an upfront fee (often via cryptocurrency) to release the victim’s “earnings.” Once paid, the money is never returned. The user’s financial and personal data can be lost in this process.
- Recruiter Phishing Flow: An attacker crafts a realistic job offer, emailing or messaging the target with a link to apply. This link goes to a spoofed site or triggers a “browser-in-browser” pop-up that looks like an official login. Any credentials entered (usernames, passwords) go straight to the attacker. Okta’s threat researchers found campaigns using over 400 spoofed domains impersonating recruiters, all designed to harvest logins for popular services
- Fake Interview Flow: In more sophisticated schemes, attackers conduct a staged technical interview. After initial recruiter outreach, the victim may receive a coding test hosted on a repository (for example, a GitHub project). When the candidate clones or runs this code, it executes hidden malware. Microsoft’s “Contagious Interview” report found victims agreeing to run malicious packages under the guise of routine coding tasks
Real-World Impact
- For individuals: the harm is immediate: financial loss and identity theft. Victims of task scams lose whatever they paid in, and sometimes more, without any real earnings. Those who entered credentials or ran malicious code may discover personal emails, social media, or bank accounts compromised. FTC reports indicate many people only realize it was a scam after significant loss.
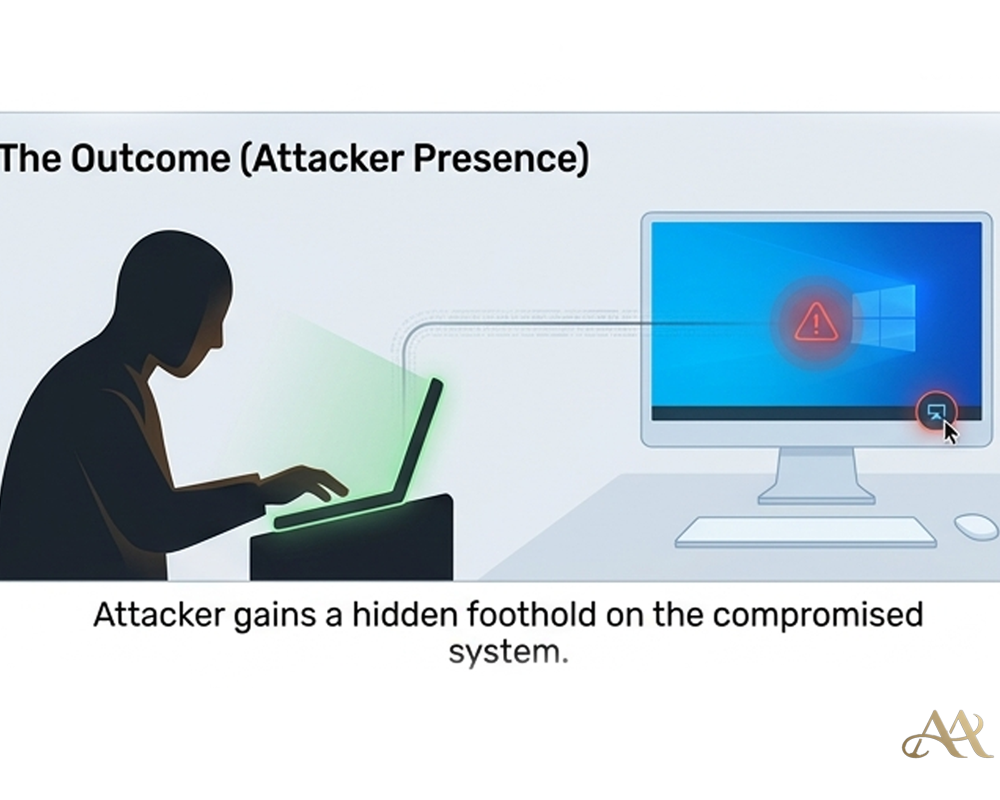
- For businesses, a compromised employee is a dangerous foothold. If a worker’s corporate login is stolen in a fake recruiter email, attackers can pivot through the network (lateral movement) and steal sensitive data or deploy ransomware. Malware from a developer’s machine can poison the software supply chain for example, Void Dokkaebi’s campaign used infected dev repos to spread malware to other projects
- On an infrastructure level, these scams fuel broader cybercrime. Scammers register hundreds of lookalike domains to impersonate companies, and they use cryptocurrencies to launder funds. The FTC notes a spike in crypto payments related to job scams, underscoring how these frauds finance other criminal activities. Public trust in online job platforms also erodes when these scams are widespread.
 Common Mistakes or Misconceptions
Common Mistakes or Misconceptions
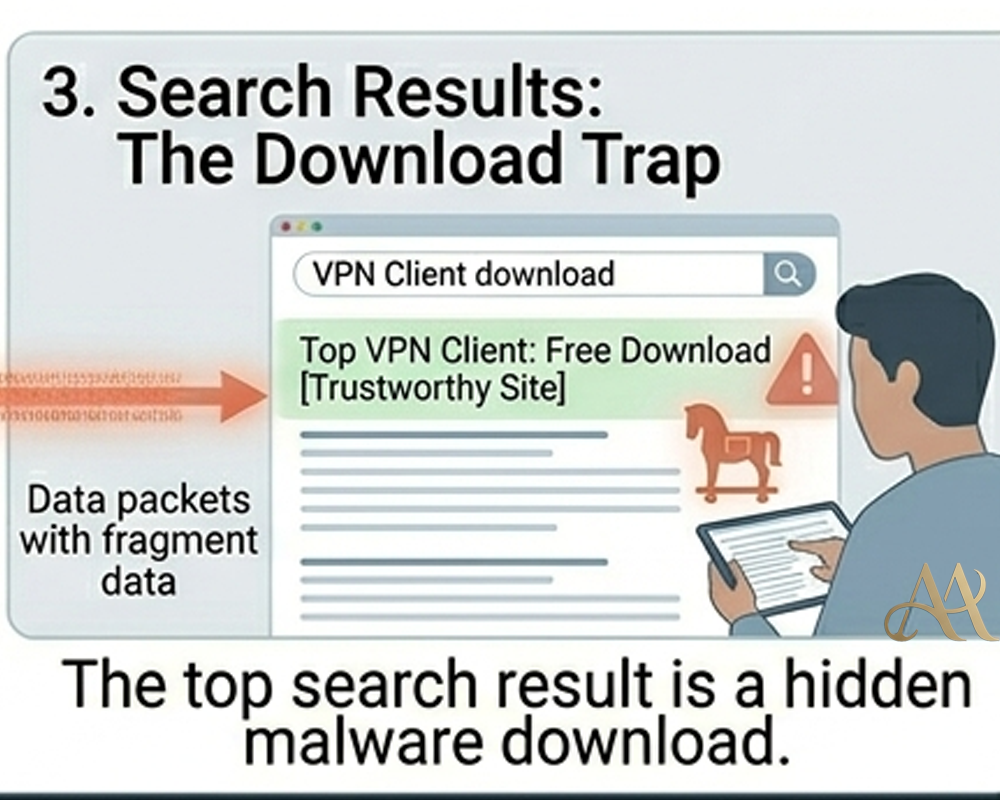
- Trusting Unexpected Offers: People often assume a LinkedIn message or email from “Google Careers” is real, especially if it looks professional. In fact, attackers can clone logos and formatting. Always verify by contacting the company through official channels or checking the actual website.
- Paying for Job Leads: Some victims believe they must pay a fee or “deposit” to secure a job or release wages. No legitimate employer asks you to pay money to earn money. If an offer requires upfront payment, it’s a scam.
- Running Unknown Code: In a fake interview, candidates might execute a provided script. This is dangerous. Legitimate technical tests should not force you to run unverified executables on your primary device. Always treat emailed attachments or code prompts with suspicion.
- Overreliance on MFA: Multi-factor authentication is important, but it’s not foolproof if attackers get you to enter one-time codes into a phishing page or run malware. MFA can mitigate credential theft but won’t stop malware already installed on your machine.
- Reusing Credentials: If you use the same password across job sites, email, and work systems, a stolen job-seeker password can let attackers try the same login elsewhere. Always use unique passwords (or a password manager) so a breach in one place doesn’t compromise all your accounts.
 Practical Defensive Measures
Practical Defensive Measures
- Verify Recruiters and Offers: Always check contact details against official company sites. If you get an unexpected job email, look up the recruiter on LinkedIn or contact the company’s HR department directly. Never follow unsolicited links; instead, navigate to the company’s career page manually.
- Treat Downloads Cautiously: For coding tests or interviews, use a sandbox or separate device. Scan downloaded files with antivirus/EDR tools before running. Enterprises can enable application control (e.g., block unknown Visual Studio Code tasks) to stop malicious scripts
- Use Strong Auth Practices: Enable unique, complex passwords and MFA on all accounts. If you feel a recruiter scam site captured your login, immediately change your password on genuine accounts. MFA (like an authenticator app) can help block unauthorized logins even if your password leaks.
- Security Training: Organizations should train employees about job-related scams. Simulate phishing tests with fake recruiter emails to build awareness. Emphasize the red flags: requests for payment, unusual login prompts, or urgent deadlines.
- Monitor and Log: Use SIEM and identity logs to detect anomalies. For example, alert on login attempts from odd locations or new OAuth apps linked to job sites. Keeping logs of recruitment emails or application traffic can help spot suspicious patterns early.
- Never Pay to Get Hired: A simple rule: “If you pay money to get a job, it’s a scam.” Treat any payment request as fraud and report it.
- Block Malicious Domains: Deploy web filters or security services that use threat intelligence. Okta’s report identified hundreds of scam domains; blocking known bad domains (and those similar to company URLs) prevents many phishing attempts.
Conclusion
Job searching is a normal and often stressful part of life, but the cyber threats in that process are very real. Attackers know that the idea of a new opportunity can make people let down their guard. By understanding the mechanics of these scams and adopting cautious habits (verify every offer, avoid suspicious downloads, use strong authentication), you can enjoy the benefits of online recruiting without falling prey to its pitfalls. Remember: if a job offer demands money or sensitive info, or asks you to run unknown code, treat it like any unexpected email – with great skepticism. In today’s threat landscape, awareness and basic security hygiene are your best defenses against recruitment scams.
REFERENCE
- https://www.ftc.gov/news-events/news/press-releases/2024/12/new-ftc-data-show-skyrocketing-consumer-reports-about-game-online-job-scams.
- Daniel, Charles & Aston, Dwight. (2024). Unmasking the Threat, Fake Job Postings Exploiting AI Technology.
- https://www.experian.com/blogs/insights/the-rising-threat-of-candidate-fraud-and-why-identity-must-come-first-in-modern-screening/



 Cyber Hygiene
Cyber Hygiene 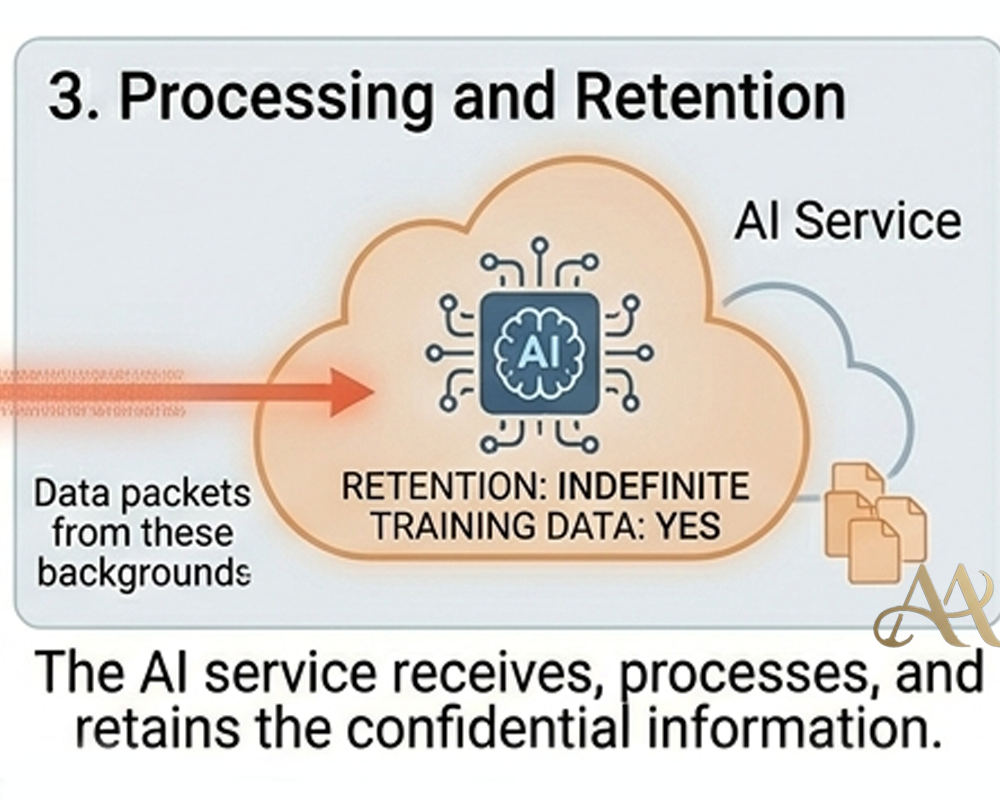 Attack Anatomy
Attack Anatomy 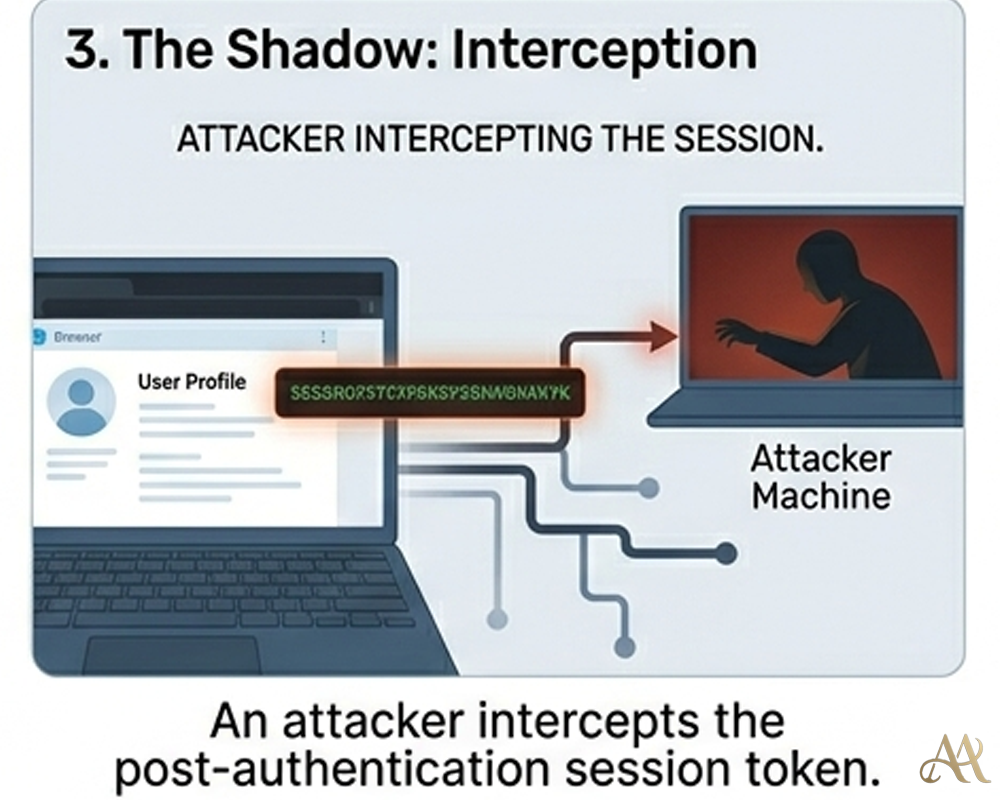

Leave a Reply