Water utilities are now prime targets for cyberattacks, meaning your tap water could be at risk. This article explains how attackers exploit water system controls and offers straightforward tips to help keep our water supply secure.
Imagine turning on the tap and finding your water contaminated or simply gone. It sounds extreme, but experts warn that water treatment plants are active cyber targets. For example, hackers cut off water to 160 homes in Ireland. This article explains why water systems are vulnerable, how attacks happen, and what simple steps (from strong passwords to network segmentation) can keep our water safe.What It Is
Water utilities use industrial control systems (ICS) rather than ordinary IT networks. Plants rely on SCADA platforms and PLCs (programmable logic controllers) to run pumps, filters, and chemical dosing. Many of these controllers connect to corporate networks or even the Internet. Since they directly control valves and pumps, attackers who access them can alter water flow or chemistry. A federal report warns that a breach could “manipulate operational technology” and disrupt clean water production.
 How It Works
How It Works
Attacks on water systems usually follow these steps:
- Initial Access: Attackers locate Internet-connected PLCs and log in. Many plants still use default or weak passwords. In one documented case, hackers used official PLC software remotely to reach a water plant’s controller.
- Taking Control: Once inside, they act like engineers. Hackers can upload malicious logic or fake sensor data. Reported incidents include wiping PLC configurations and disabling operator screens (HMIs), which can halt pumps or alarms.
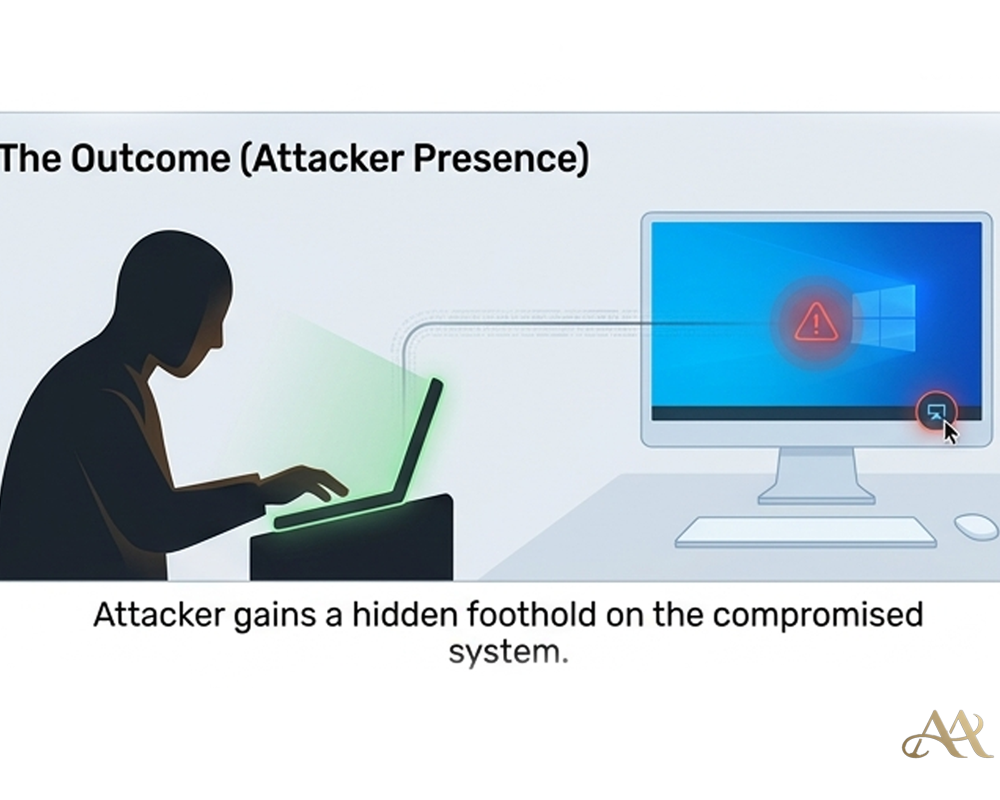
- After compromising one device, attackers create backdoors. If the plant’s IT and OT networks are connected, they can steal credentials and jump between systems. This lets them spread deeper until discovered.
 Real-World Impact
Real-World Impact
Cyberattacks on water systems can hit communities hard:
- Individuals and Communities: A cyber breach could make tap water unsafe or cut it off entirely. Even short outages force emergencies – for example, 160 homes in Ireland lost water in one attack.
- Businesses andInfrastructure: Water is vital for industries, hospitals, and firefighting. If a plant shuts down, services halt. For instance, when the Colonial Pipeline was hacked, fuel deliveries nationwide stopped. A similar outage of a water system could paralyze a city.
In short, attacks on water infrastructure aren’t just about stolen data – they can become public health and safety crises.
Common Mistakes or Misconceptions
Even well-intended utilities can overlook key risks:
- Assuming Air-Gap: Many believe water plants are offline and safe. In reality, most have some network connections. Thinking “it can’t happen here” leaves dangerous blind spots.
- Default or Weak Passwords: Controllers often ship with default credentials. CISA found many PLCs still using the default “1111”. Leaving such passwords unchanged is an open invitation to hackers.
- Underestimating Small Utilities: There are thousands of small, under-resourced water plants. A breach that a large city might absorb could cripple a tiny town.
Recognizing and correcting these misconceptions is the first step to stronger security.
 Practical Defensive Measures
Practical Defensive Measures
Water utilities can take concrete, effective steps to reduce risk:
- Segment Networks: Isolate control systems behind firewalls or gateways. Deny direct Internet access to PLCs. If remote maintenance is needed, route it through secure jump servers.
- Strong Authentication and Patching: Change default passwords and use strong, unique credentials. Enable multi-factor authentication for any remote access. Keep PLC firmware and SCADA software updated.
- Monitor and Plan: Continuously monitor OT systems for anomalies. Have an incident response plan specific to water (for example, how to isolate the plant and switch to manual controls).
Many recommended defenses are straightforward and procedural. For example, the EPA provides free cybersecurity assessments and training for water utilities, noting that many fixes (better passwords, clearer procedures) are far cheaper than replacing equipment.
Conclusion
A cyber breach of a water plant is effectively a public health emergency. Recent incidents make it clear that water infrastructure is targeted. The good news is that many defenses are straightforward: strong passwords, segmented networks, updated systems, and vigilant monitoring can all make a big difference. Communities that apply these measures can keep their taps safe. Cybersecurity for water ultimately means protecting public health and safety.
REFERENCE
- https://www.des.nh.gov/news-and-media/blog/cybersecurity-water-sector-are-you-risk
- https://www.iwmi.org/news/cybersecurity-risks-are-rising-for-water-utilities-heres-why/




 Cyber Hygiene
Cyber Hygiene  Attack Anatomy
Attack Anatomy 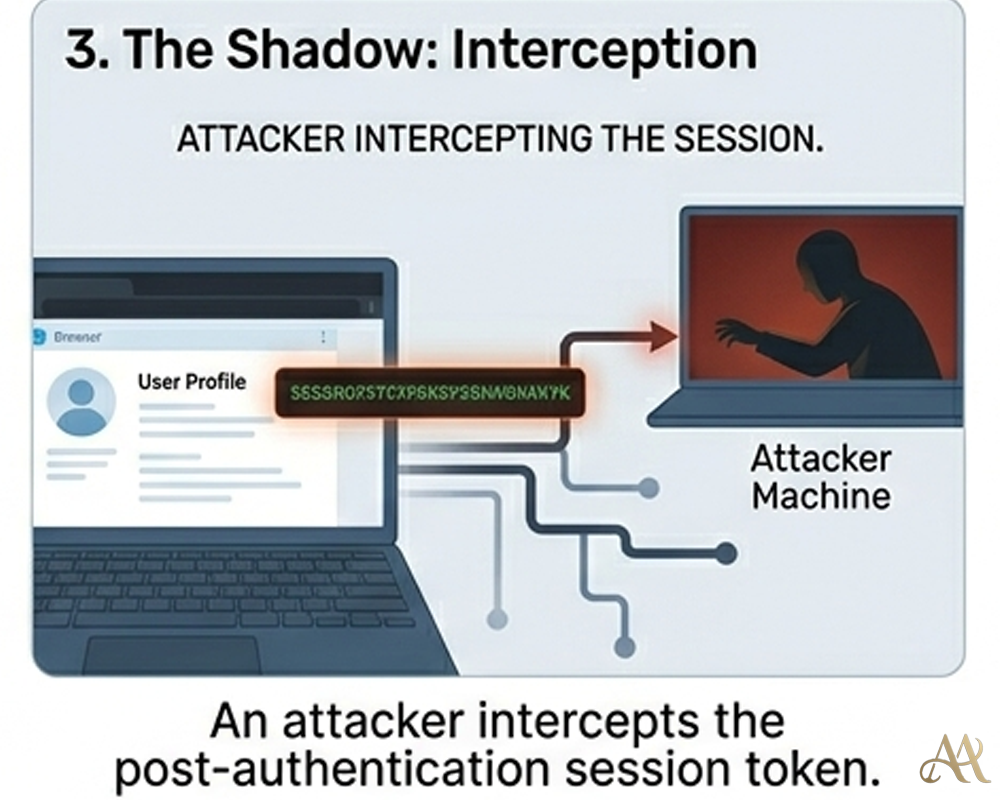
Leave a Reply