Your phone number is often used as proof of identity, but attackers can take it over through SIM swapping or port-out fraud. Here is how the attack works and how to reduce the risk.
Imagine waking up and your phone suddenly has no service. No calls. No texts. No data. Then you try to log in to your email or bank account, but the verification codes are no longer coming to you.
That is the danger of SIM swapping and port-out fraud. Many online services still treat your phone number as proof that you are you. The problem is that your phone number is not fully under your control. A criminal may not need your physical phone if they can convince a carrier to move your number to a SIM or account they control.
This matters now because SIM Swap is tracked as its own category in the FBI’s 2025 IC3 report, with 971 complaints and more than $17 million in reported losses. The broader issue is bigger than the number itself: phone numbers are still used to reset passwords, receive SMS codes, and approve account access.
 This article explains how phone-number takeover works, why SMS-based authentication is weaker than many people think, and what practical steps can reduce the risk.
This article explains how phone-number takeover works, why SMS-based authentication is weaker than many people think, and what practical steps can reduce the risk.
What It Is
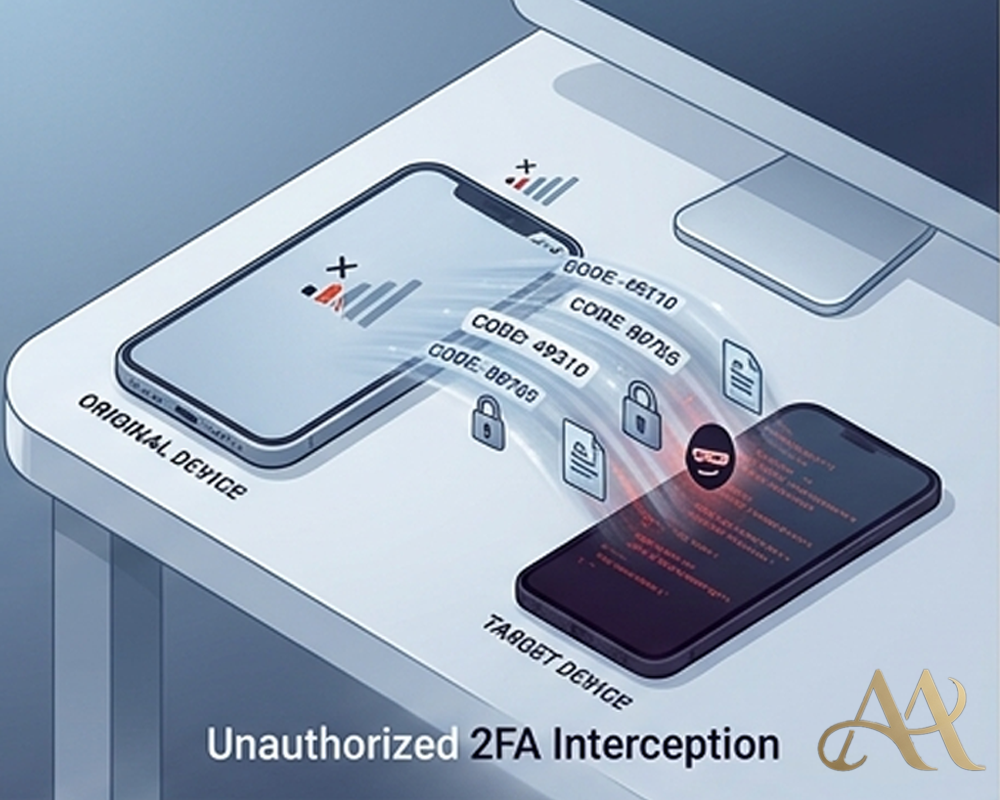
SIM swapping is a form of account takeover where an attacker tricks or convinces a mobile carrier to transfer a victim’s phone number to a SIM card controlled by the attacker. Port-out fraud is similar, but instead of moving the number to a new SIM on the same carrier, the attacker transfers the number to another carrier account they control.
The Federal Communications Commission describes SIM swapping as a fraudulent transfer of service from the victim’s phone to a phone in the bad actor’s possession. It describes port-out fraud as a scenario where the attacker poses as the victim and transfers the phone number to a different carrier controlled by the attacker.
In simple terms, the attacker is not stealing your phone. They are stealing the identity layer attached to your phone number.
That matters because many services use your number for password resets, one-time codes, fraud alerts, account recovery, and identity verification.
How It Works
- Reconnaissance: The attacker first gathers personal details about the target. This may include full name, phone number, date of birth, address, leaked passwords, email address, or answers to security questions. These details may come from phishing, breached databases, social media, or data brokers.
- Carrier Manipulation: The attacker contacts the mobile carrier and pretends to be the victim. They may claim the phone was lost, damaged, or upgraded. The FTC explains that scammers may ask the provider to activate a new SIM card connected to the victim’s phone number on a phone the scammer owns.
- Number Takeover: If the carrier approves the request, the victim’s phone loses service. At that point, the attacker receives calls and text messages meant for the victim.
- Account Access: The attacker then tries to reset passwords or request SMS verification codes from email, banking, cryptocurrency, social media, or cloud accounts. This is where the phone number becomes dangerous. It acts like a security key, even though the victim did not approve the transfer.
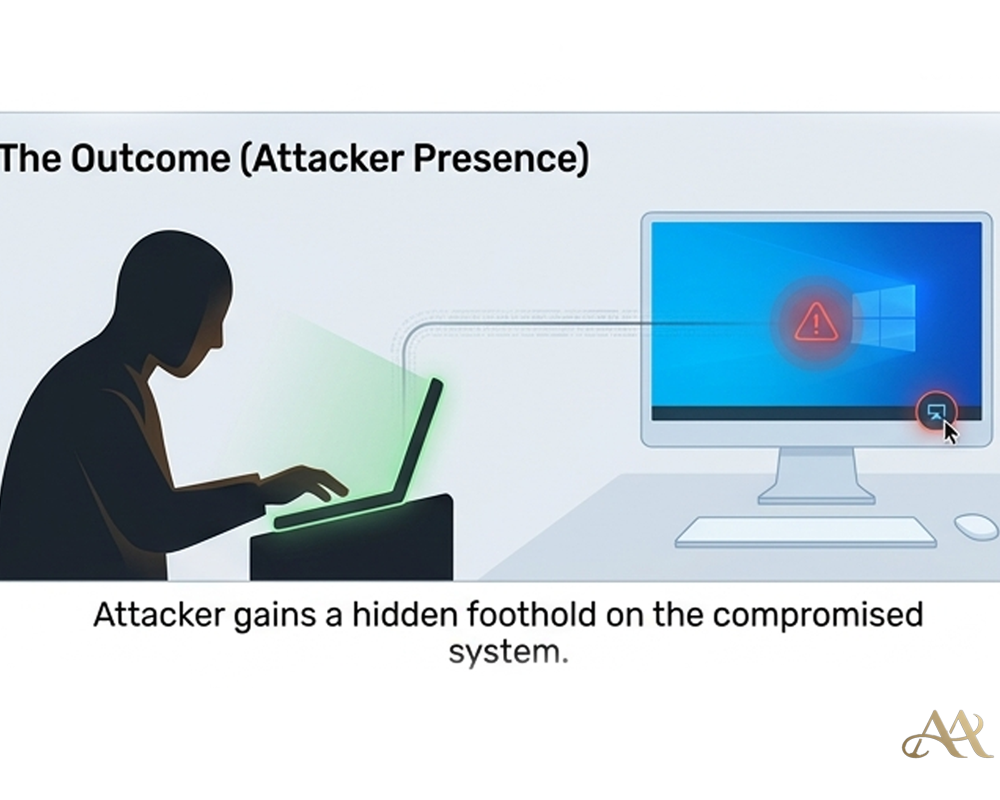
- Post-Compromise Activity: Once inside an account, the attacker may change passwords, add recovery emails, move money, steal data, or lock the victim out. In MITRE ATT&CK terms, the social engineering stage aligns with Phishing (T1566), while the use of stolen or reset credentials can align with Valid Accounts (T1078).
Real-World Impact
- For individuals, the impact can be immediate. A stolen number can expose email, bank accounts, cryptocurrency wallets, social media accounts, and personal records. The first warning sign may simply be that the phone stops working.
- For businesses, SIM swapping can affect executives, finance staff, IT administrators, and employees with privileged access. If attackers take over a phone number tied to corporate email or cloud access, they may gain a route into business systems.
- For systems and infrastructure, the problem is identity trust. Security tools may see a successful login using a valid code, not an obvious intrusion. That makes detection harder for SOC teams unless identity logs, device changes, impossible travel, and account recovery activity are monitored in the SIEM.
Common Mistakes or Misconceptions
- Believing your phone number is private: Most phone numbers are widely shared. They appear in forms, delivery records, social profiles, business directories, and breached datasets.
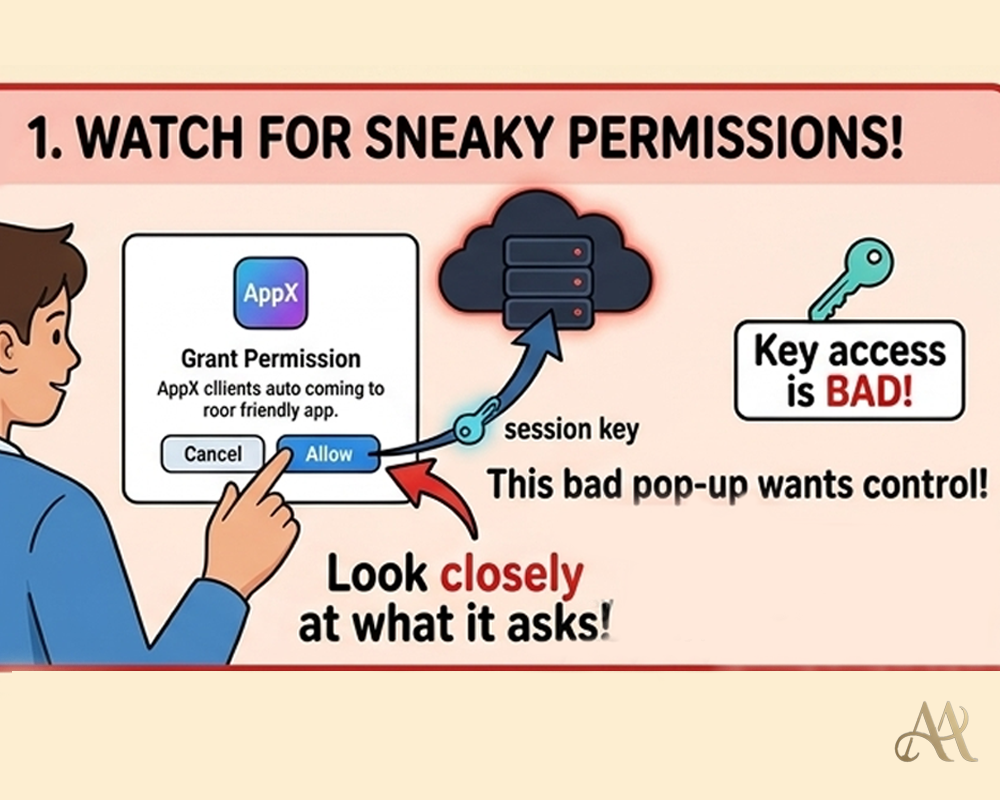
- Trusting SMS as strong MFA: SMS is better than no MFA, but it is weaker than authenticator apps, passkeys, or hardware security keys. The FTC specifically advises that text message verification may not stop a SIM swap and suggests using an authentication app or security key for sensitive accounts.
- Ignoring sudden loss of service: If your phone suddenly loses service without explanation, treat it as a security incident, not just a network problem.
- Using the same number for everything: When one phone number controls banking, email, password resets, and social accounts, compromise of that number can become a chain reaction.
Practical Defensive Measures
- Start with your mobile carrier. Set a strong account PIN or port-out protection if your provider offers it. Avoid using easily guessed information such as birthdays, repeated numbers, or old addresses.
- Move important accounts away from SMS-based authentication. Use authenticator apps, passkeys, or hardware security keys for email, banking, cloud platforms, and cryptocurrency accounts.
- Protect your primary email account first. If attackers control your email, they can reset many other accounts. Use strong MFA, recovery codes, and a unique password stored in a password manager.
- Reduce public exposure of personal details. Avoid posting your full phone number, address, date of birth, and carrier information online.
- For organizations, classify SIM swap as an identity risk. Require stronger MFA for privileged users. Monitor for account recovery events, new devices, new MFA methods, and logins after phone-number changes. High-value staff should not rely on SMS for administrative access.
If your number is taken over, contact your carrier immediately, recover the number, change passwords, check financial accounts, revoke suspicious sessions, and review account recovery settings.
Conclusion
Your phone number was designed for communication, not high-assurance identity. Yet many systems still treat it as proof that you are the rightful user.
That gap is what SIM swapping exploits. Attackers do not always need to break encryption or steal your device. Sometimes they only need to move your number.
The lesson is simple: protect your number, but do not rely on it as your strongest security control. In modern cybersecurity, the safest identity systems are the ones that do not depend on a phone number alone.
REFERENCE
- https://www.ic3.gov/annualreport/reports
- https://www.fbi.gov/contact-us/field-offices/phoenix/news/press-releases/fbi-tech-tuesday-sim-swapping
- https://www.ic3.gov/PSA/2022/PSA220208



 Cyber Hygiene
Cyber Hygiene 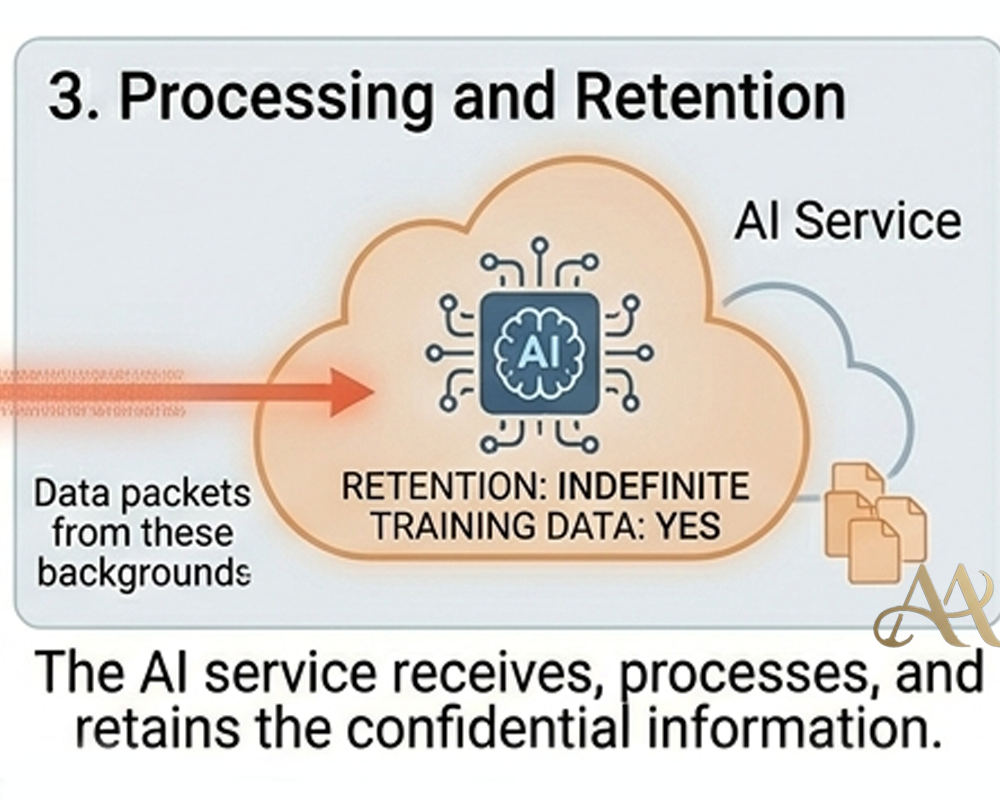 Attack Anatomy
Attack Anatomy  Digital Deception
Digital Deception 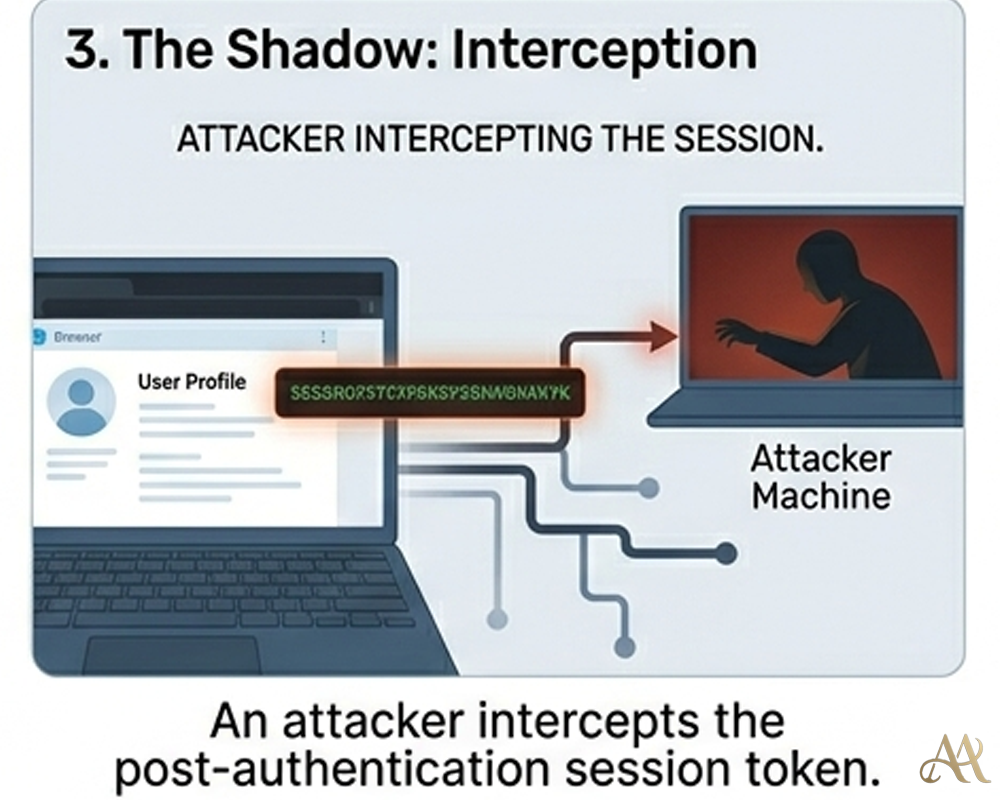

Denise Jun 02, 2026 at 2:36 PM
Thank you for the wonderful article. It is very educative