Cyberattacks on hospitals are no longer hypothetical, they delay care, expose data, and endanger lives. This article explains how and why these attacks happen and what healthcare organizations can do to protect patients.
Imagine calling 911 and being told the nearest hospital is offline. It sounds like a dystopian scenario, but it’s happening today. Cyberattacks on hospitals are no longer just data breaches; they disrupt care and even endanger lives. Global agencies warn that healthcare has become one of the most targeted critical sectors. In this article, you’ll learn why hospital cyberattacks are a public-health issue, how these attacks work, and what providers and patients can do about them.
What It Is
A hospital cyberattack involves hackers exploiting vulnerabilities in a healthcare organization’s IT systems. These attacks can take many forms, ransomware, data breaches, or attacks on medical devices but they share one goal: to cripple the hospital’s ability to provide care or steal sensitive data. Key terms include electronic health records (EHR) (the digital files of patient data), ransomware (malware that encrypts systems for ransom), and medical devices (like connected monitors or imaging machines). In simple terms, these attacks turn computers and networks against the hospital itself, blocking nurses’ and doctors’ tools or leaking patients’ private records.
How It Works
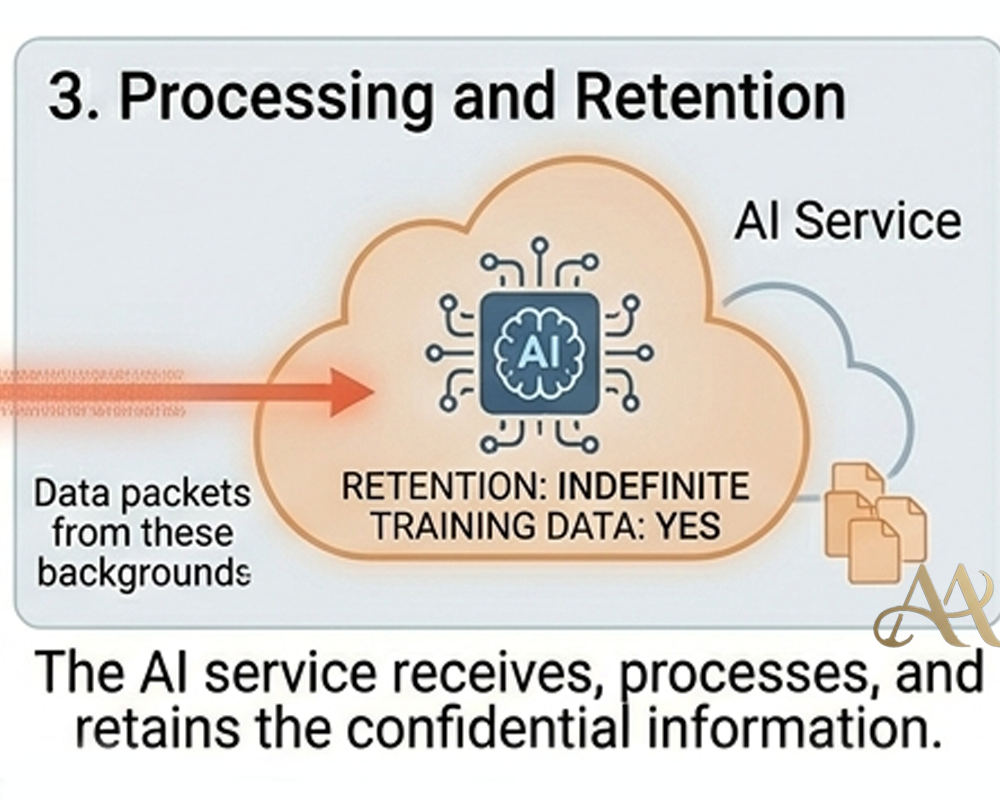
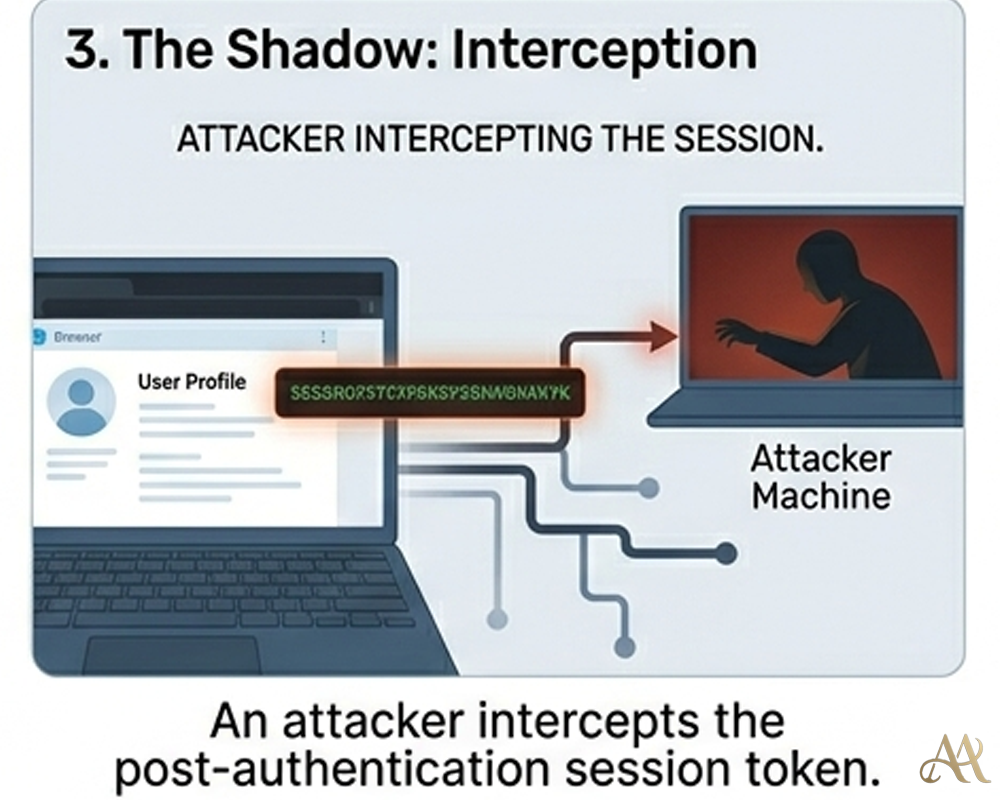
Most hospital attacks start with everyday tricks. For example, an email phishing campaign (MITRE ATT&CK T1566) might lure a staff member into clicking a malicious link. Once the hacker gains an initial foothold, they often use credential theft or exploit unpatched software to move laterally through the network (ATT&CK T1078 for account misuse, T1210 for exploitation). Attackers may then deploy ransomware (ATT&CK T1486), encrypting file servers or EHR systems. This locks doctors and nurses out of patient charts, scheduling, and even medical devices.
In one scenario, an attacker might break into the hospital network via an unpatched server or stolen login, escalate privileges to gain administrative control, and push a ransomware payload to all connected systems. Some attacks also exfiltrate data before encrypting it (ATT&CK T1567), threatening to leak sensitive records if the ransom isn’t paid. Throughout the incident, defenders see few obvious alerts: the malicious activity looks like legitimate user traffic in the network (bypassing MFA) and often triggers only after systems are already compromised.
Real-World Impact
When hospital systems go dark, the consequences are immediate and human. For patients, cyberattacks can delay diagnoses and treatment. For example, a 2020 ransomware attack in Germany forced emergency patients to be diverted to other hospitals; one patient died en route. In the recent Massachusetts case, Signature Healthcare had to divert ambulances and cancel chemotherapy infusions, even closing pharmacies after its network was hit. These disruptions can literally be a matter of life and death.
- For healthcare organizations, the fallout is both operational and financial. Routine appointments and surgeries are postponed; in one case, a major U.S. hospital network took systems offline, delaying thousands of procedures and even diverting ambulances. Hospital staff must revert to paper charts and manual processes, slowing down care. Breached records risk patient privacy and regulatory penalties. A WHO/Europe report notes that cyber breaches can “delay treatments and even endanger the lives of patients”. Rebuilding IT systems after such an attack can cost millions in downtime and lost trust.
- For infrastructure, the ripple effects are severe. Critical devices and systems—like electronic health records, imaging machines, or even drug-dispensing robots—can be taken offline or manipulated. The 2017 WannaCry outbreak, for example, infected diagnostic equipment across the UK’s NHS, forcing ambulances to divert and 19,000 appointments to be canceled. Cyberattacks may also shut down entire hospital wings and force “code black” emergency statuses, illustrating that a cyber incident can become a true public-health crisis.
Common Mistakes or Misconceptions
A common misconception is that hospitals are too specialized to be targeted by generic cyberattacks. In reality, cybercriminals know healthcare is a high-value target because lives and the pressure to resolve incidents quickly are on the line. Another mistake is assuming antivirus or basic firewalls alone are sufficient. Many breaches actually begin with simple human errors or unpatched systems, not highly sophisticated zero-day exploits.
Some organizations also believe that having backups or cyber insurance makes an attack harmless. But backups need to be isolated and frequently tested to work under attack, and insurance payouts don’t restore patient trust or guarantee devices come back online. Finally, there’s a tendency to treat cybersecurity as an IT issue only; in hospitals it must be part of patient safety planning. As the American Hospital Association emphasizes, cyber risks are patient safety risks
Practical Defensive Measures
Protecting hospitals requires both technical controls and planning. First, network segmentation is crucial: separate critical systems (like EHR servers and medical devices) from the rest of the network. This limits lateral movement if an attacker gains access. Implement strong authentication (MFA) for all remote and administrative access, and monitor login attempts for anomalies in a SIEM. Keep all systems especially medical devices and legacy machines patched and up to date. Because medical devices often lack built-in security, hospitals should maintain an accurate inventory and apply compensating controls (such as access control lists).
Healthcare providers should also enforce offline, regular backups of all patient data and critical applications. These backups must be tested by attempting restores, ensuring that systems can be brought back online quickly if encrypted. Develop and rehearse an incident response plan that includes clinical staff so that patient care can continue (for example, fallback to manual processes and clear communication strategies during downtime). As part of planning, hospitals may coordinate with local EMS and other nearby facilities to handle ambulance diversions.
On the detection side, deploy Endpoint Detection and Response (EDR) tools and continuously log network traffic for signs of command-and-control (C2) activity or unusual file encryption. Establish a dedicated cybersecurity team or leader focused on risk to patient safety (as recommended by WHO and AHA). Finally, educate all staff, clinicians, administrators and technicians, about phishing and cyber hygiene: human awareness is often the first line of defense.
Conclusion
Cyberattacks on hospitals are no longer abstract tech news, they are public-health emergencies in the making. The examples of diverted ambulances, canceled surgeries, and even patient deaths make this all too clear. As healthcare systems become ever more digital, defenders must treat cybersecurity as integral to patient safety. By understanding how attacks unfold and preparing systems and staff, hospitals can help ensure that patients’ health and lives remain secure in the face of rising cyber threats.
- https://www.who.int/news-room/questions-and-answers/item/cyber-attacks-on-critical-health-infrastructure
- https://www.aha.org/news/headline/2026-04-10-fbi-health-care-was-top-target-ransomware-other-cyberthreats-2025




 Cyber Hygiene
Cyber Hygiene  Digital Deception
Digital Deception 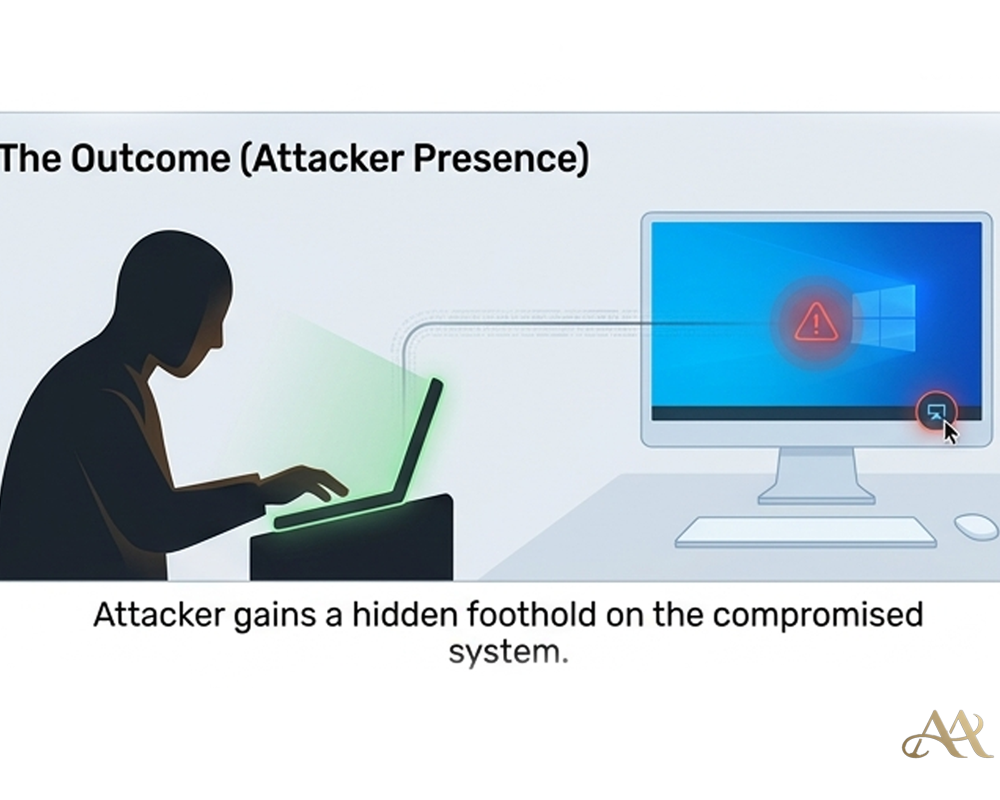
Leave a Reply