Attackers no longer need your password, they need your session. Learn how session hijacking bypasses MFA and what you can do to stay protected.
For years, cybersecurity advice has focused on one thing: protect your password. Use strong passwords, avoid reuse, and enable multi-factor authentication (MFA). That guidance is still valid but it is no longer enough. Attackers have adapted. Instead of trying to break into your account, they are increasingly stealing what comes after login: your session. If you have ever logged into a website and remained signed in without re-entering your password, you have used a session. That convenience is now being exploited.
This article explains what session hijacking is, how attackers steal session tokens, why this technique bypasses traditional defenses like MFA, and what practical steps can reduce the risk.
 What a Session
What a Session
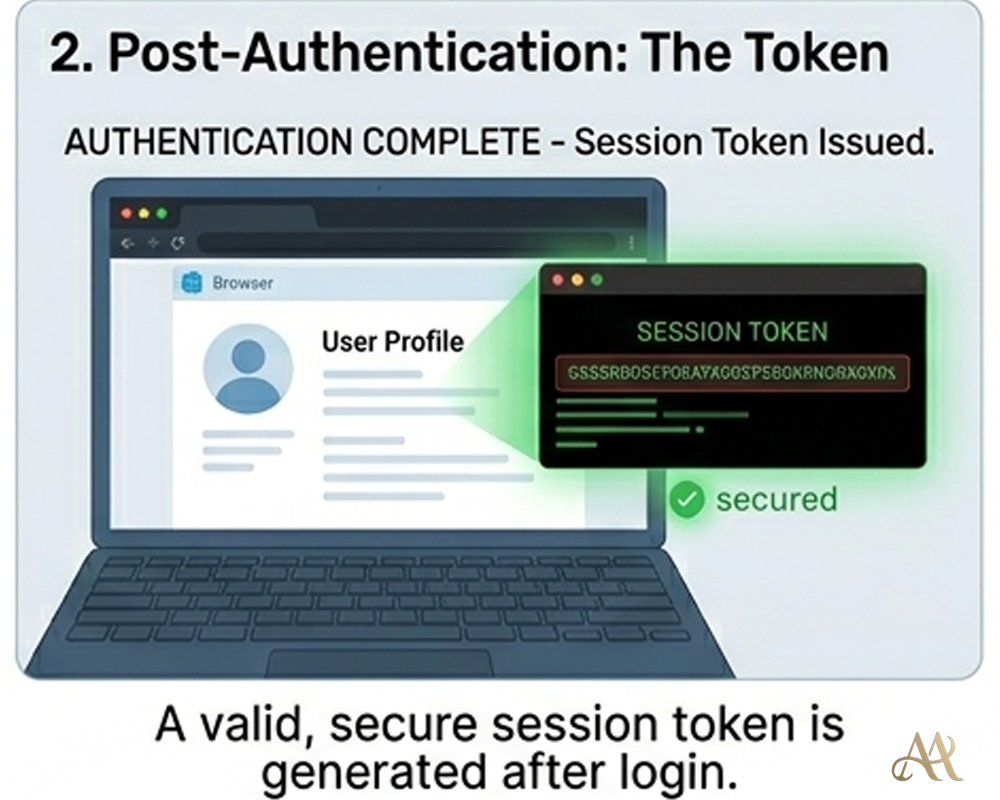
A session is the mechanism that keeps you authenticated after logging in. Instead of asking for your password on every request, a website issues a session token often stored in your browser as a cookie. This token acts as proof that you have already authenticated.
In simple terms:
- Password = how you log in
- Session token = how you stay logged in
Attackers have realized that stealing the session token can be more efficient than stealing the password itself. If they obtain a valid session token, they can impersonate the user without needing credentials or triggering MFA.
This technique is commonly referred to as session hijacking or session theft.
How It Works
- Initial access: The attack usually starts with phishing, malware, a malicious browser extension, or endpoint compromise. This gives the attacker a foothold on the user’s device or browser environment. In MITRE ATT&CK, this can align with Phishing (T1566) or other initial access techniques.
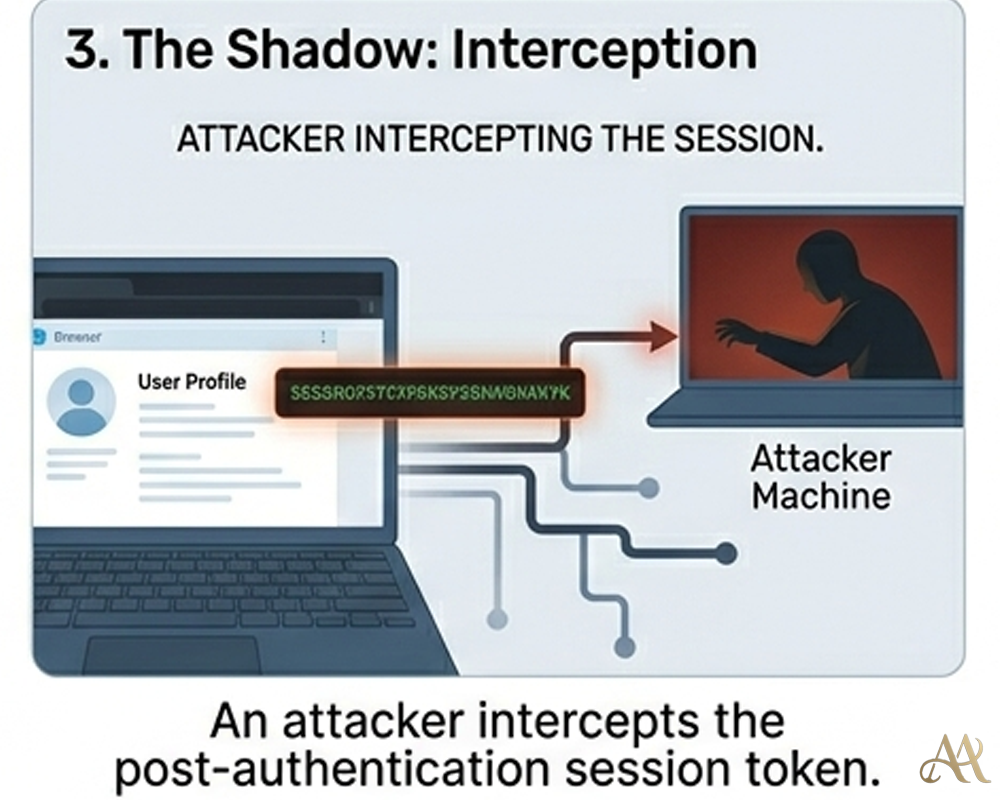
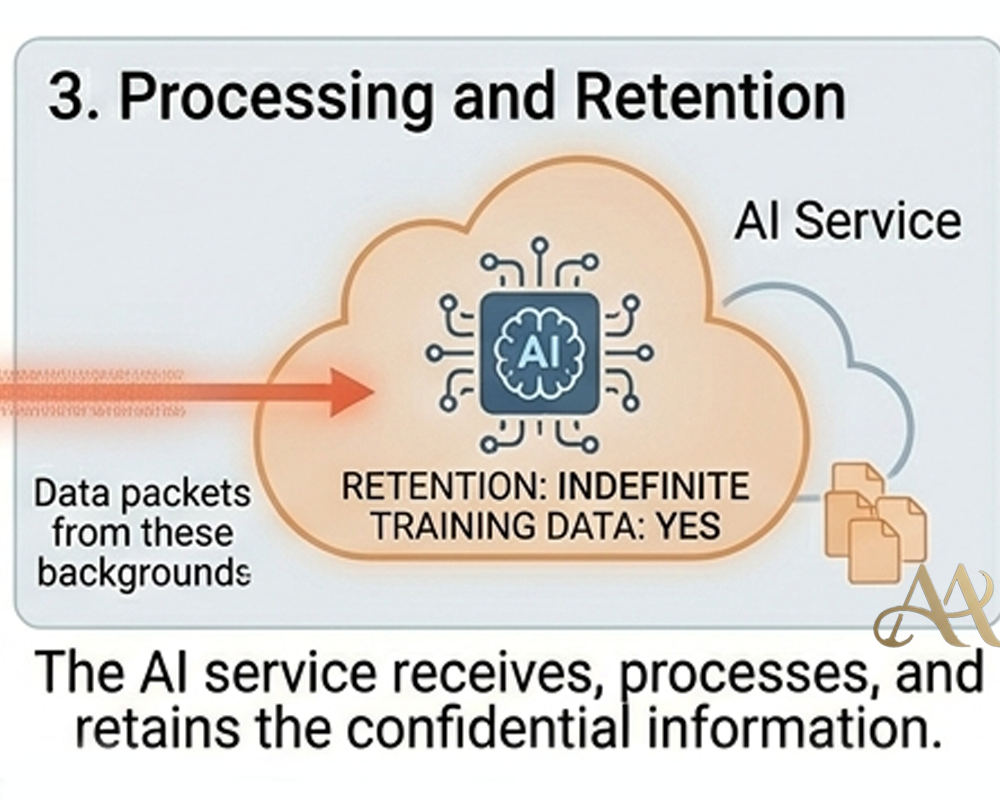
- Session token extraction: Once the attacker has access to the device or browser, malware or scripts can extract session cookies and authentication tokens. These tokens may belong to services such as email, cloud platforms, collaboration tools, banking portals, or enterprise applications.
- Token reuse: The attacker then imports or replays the stolen session token in their own environment. Because the token represents an already authenticated session, the attacker may not need the victim’s password or MFA code.
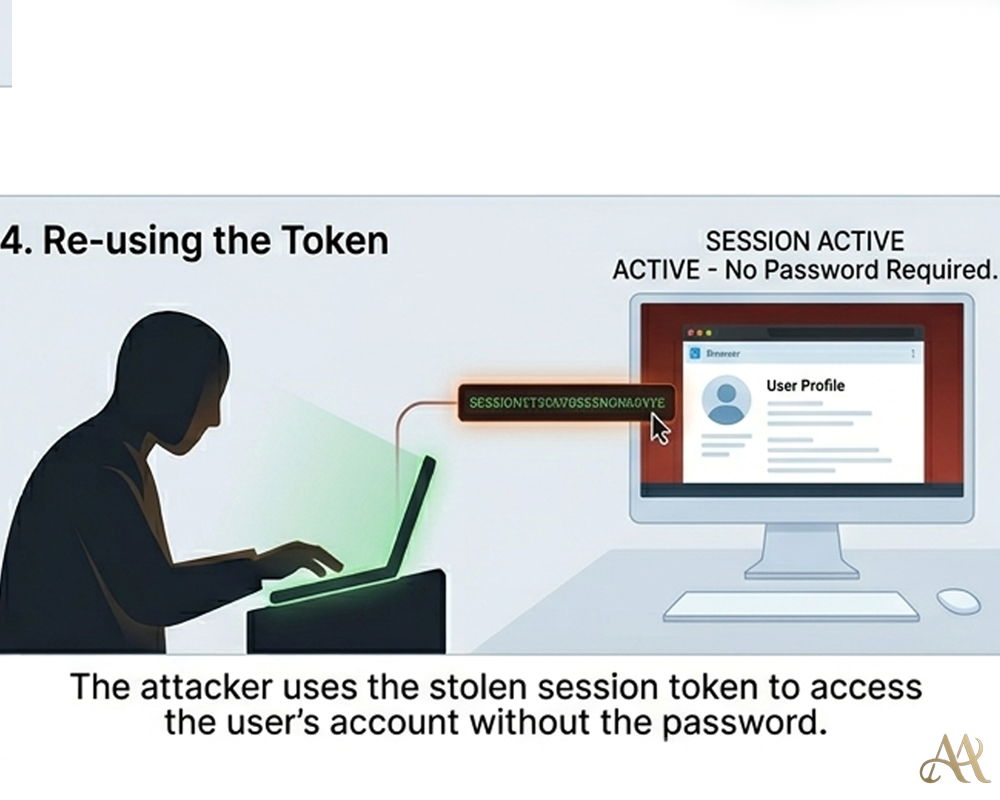
- Account access and persistence: With a valid session, the attacker can act as the user. They may read sensitive data, send messages, change account settings, create new access methods, or add persistence mechanisms such as backup emails, new MFA devices, or application passwords.
- Post-exploitation activity: After gaining access, the attacker may move deeper into the environment. This can include privilege escalation, lateral movement across systems, data theft, or command-and-control communication.
- Detection challenge: Session theft is difficult to detect because the activity can look like normal authenticated user behavior. The SOC may not see failed logins or MFA prompts; instead, it may only see a valid session performing unusual actions.
 Real-World Impact
Real-World Impact
- Individuals can lose access without seeing a normal login alert: A compromised session can let attackers access email, social media, banking, or cloud accounts without entering the password again. Because the session is already trusted, the victim may not receive the usual MFA prompt or failed-login warning.
- Businesses face serious cloud and SaaS exposure: Session theft is especially dangerous when the hijacked session belongs to an administrator, finance user, developer, or executive. With that access, attackers may read sensitive data, change configurations, create new accounts, add backdoors, or abuse trusted SaaS platforms.
- Security teams lose important detection signals: Traditional alerts such as failed login attempts, suspicious password resets, or repeated MFA challenges may not appear. Instead, the SIEM may only show an already-authenticated session performing actions that look legitimate unless behavior monitoring is in place.
- Infrastructure risk increases after access is established: If the stolen session connects to internal tools, cloud consoles, identity providers, or remote access platforms, the attacker may move deeper into the environment. This can support privilege escalation, lateral movement, data theft, or long-term persistence.
Common Mistakes or Misconceptions
- Believing MFA fully protects the account: MFA protects the login process, but it does not automatically protect an already-authenticated session. If the attacker steals a valid session token after login, MFA may no longer be part of the access flow.
- Thinking there is no breach if the password was not stolen: This is an outdated assumption. Session theft can give attackers account access without ever knowing the password.
- Assuming only executives or high-value users are targeted: Session hijacking can affect ordinary users too, especially through infostealer malware, malicious browser extensions, phishing kits, and compromised personal devices. Any valid session can become useful to an attacker.
- Relying on occasional logout as the main defense: Logging out can reduce exposure, but it is not enough by itself. Many users stay logged in for long periods, and some stolen tokens remain useful until revoked, expired, or blocked by security controls.
 Practical Defensive Measures
Practical Defensive Measures
- Protect the endpoint first: Session theft often starts with malware, infostealers, or malicious browser extensions on the user’s device. Use EDR to detect suspicious behavior, keep systems patched, and investigate signs of browser credential or cookie theft.
- Use conditional access policies: Do not trust a session only because it is valid. Evaluate device trust, user location, login risk, impossible travel, and whether the device is managed before allowing access to sensitive systems.
- Monitor session behavior in the SIEM: Send authentication, cloud activity, and identity logs into your SIEM. Look for unusual geolocation changes, simultaneous sessions from distant regions, suspicious API activity, abnormal downloads, or changes to MFA and recovery settings.
- Reduce session lifetime where possible: Shorter session lifetimes limit how long a stolen token remains useful. For sensitive systems, avoid long-lived sessions and require periodic revalidation.
- Apply least privilege access: Users should only have the access they need to perform their roles. If a session is hijacked, least privilege reduces what the attacker can reach or change.
- Secure browser environments: Restrict risky browser extensions, review extension permissions, and block unauthorized add-ons where possible. Malicious extensions can read browsing activity, steal cookies, and capture session data.
- Require re-authentication for sensitive actions: Do not allow high-risk actions only because a user is already logged in. Require fresh MFA or credential confirmation before changing passwords, adding MFA devices, exporting data, modifying payment settings, or creating privileged accounts.
Conclusion
Cybersecurity has long focused on protecting passwords. That focus is still necessary, but it is no longer sufficient. Attackers have shifted their attention to session tokens the invisible mechanism that keeps users logged in. By stealing sessions, they bypass traditional defenses and operate under the identity of legitimate users. The implication is clear: authentication is no longer a single event. It is a continuous process that must be monitored, validated, and controlled. Understanding this shift is critical. Because in today’s threat landscape, protecting the login is only part of the problem the real risk begins after access is granted.
REFERENCE
- https://www.fbi.gov/contact-us/field-offices/atlanta/news/cybercriminals-are-stealing-cookies-to-bypass-multifactor-authentication
- https://www.obsidiansecurity.com/blog/session-hijacking-how-it-works-how-to-stop-it




 Cyber Hygiene
Cyber Hygiene  Digital Deception
Digital Deception 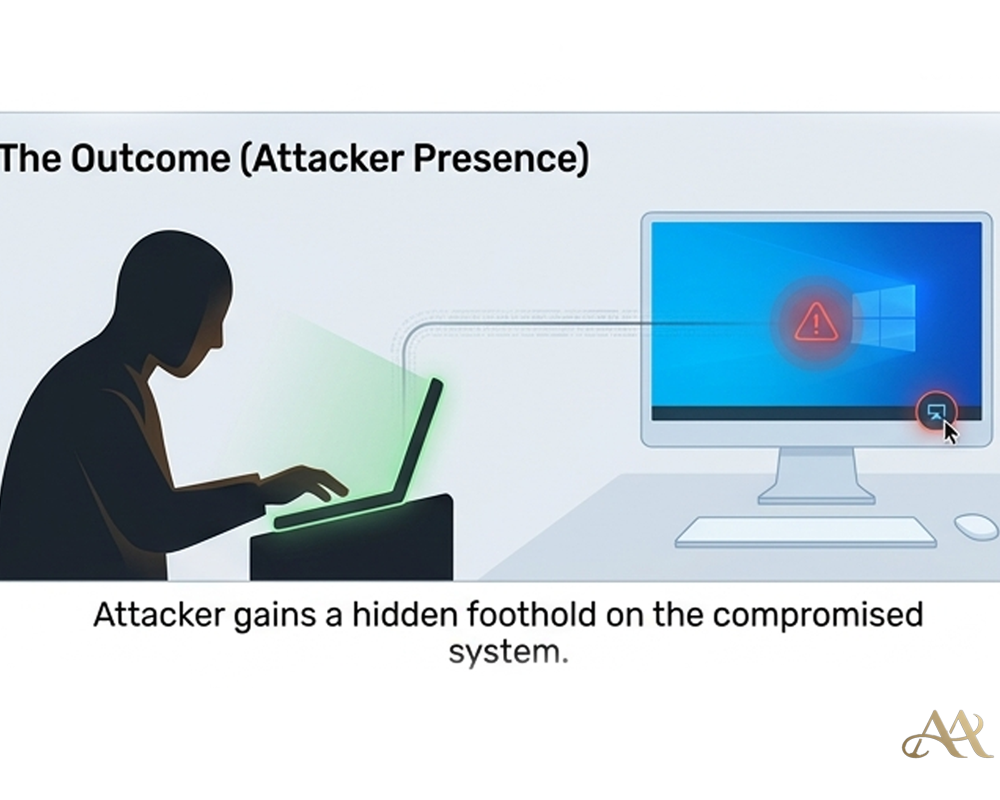
Leave a Reply